“Data security refers to protective digital privacy measures that are applied to prevent unauthorized access to computers, databases and websites and to also protect data from corruption.”
Data security is an essential aspect of IT for organizations of every size and type. With the growing cases of data security breach it has become an issue of utmost importance. Companies like Facebook and Google have also had their chance of encounter with massive data breaches.

An Indian security researcher,Laxman Muthiyah while investigating how Instagram lets its users access their account incase they forget their password found a bug in the app’s account recovery process that could’ve allowed hackers to break into people’s account.
To prove your identity, Instagram sends a six-digit passcode (that expires after 10 minutes) to your registered smartphone which needs to put in the app to confirm one’s identity.
This means, that anyone could brute force the process by inputting a million combinations to unlock an Instagram account. But it is not that simple because Instagram has certain restrictions on inputting codes into the account recovery process. They include rate-limiting the number of guesses to 250 per IP address and also the guesses must be made within a 10-minute window.
However, according to Muthiyah, Instagram’s rate-limiting feature can be bypassed by sending a huge amount of requests from various IP addresses and by sending multiple requests to process simultaneously.
Muthiyah also uploaded a video to demonstrate how he used ‘brute-force’ attack to break into Instagram’s account recovery process. The video shows him sending 200,000 guesses to break into an Instagram test account.
“Instagram forgot password endpoint is the first thing that came to my mind while looking for an account takeover vulnerability. I tried to reset my password on the Instagram web interface. They have a link-based password reset mechanism which is strong, and I couldn’t find any bugs after a few minutes of testing. Then switched to their mobile recovery flow, where I was able to find a susceptible behaviour,” Muthiyah said in a post.
Meanwhile, in a statement, Instagram said that the bug has been fixed. “We have fixed the issue and found no evidence of misuse. We’re grateful to the researcher for his help in identifying the issue, ” said the company.
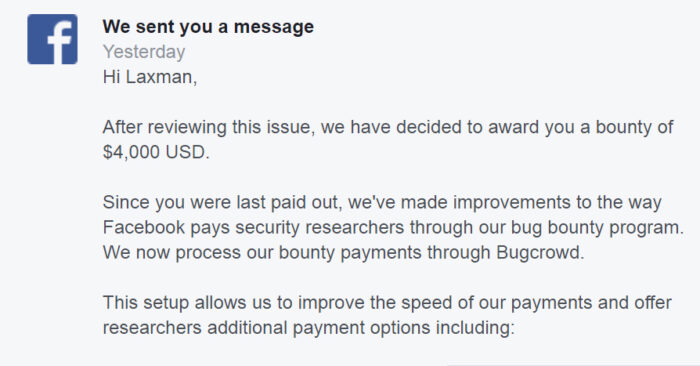
Muthiyah has also been awarded $40,000 under Facebook’s bug bounty program ‘Bugcrowd’ for finding the vulnerability.